
In the world of Cyber Security, Essential Eight is a term that is frequently heard. It’s a set of security strategies that businesses can implement to protect themselves against cyber threats. But have you ever wondered why Essential Eight was created in the first place?
Essential Eight was created by the Australian Cyber Security Centre, also known as the ACSC, in response to the increasing frequency and severity of cyberattacks on Australian businesses. The ACSC recognised that the majority of cyberattacks could have been prevented or mitigated if businesses had implemented basic security measures.
Essential Eight was originally developed to give Australian governmental agencies, departments, councils and other businesses in the public sector a framework to increase their security and operational practices. These strategies are now highly recommended for all private businesses as a foundation for their Cyber Security controls so that Australian businesses are protected against cybercrime as cybercriminals develop and improve their attacks.
At the moment, with the current rate of cyberattacks, businesses should aim at getting the security basics right. After analysing factors like the incident response of some of the early victims of cyberattacks, the ACSC released a revised 2023 version of its Essential Eight Strategies to Mitigate Cyber Security Incidents, originally released in 2017.
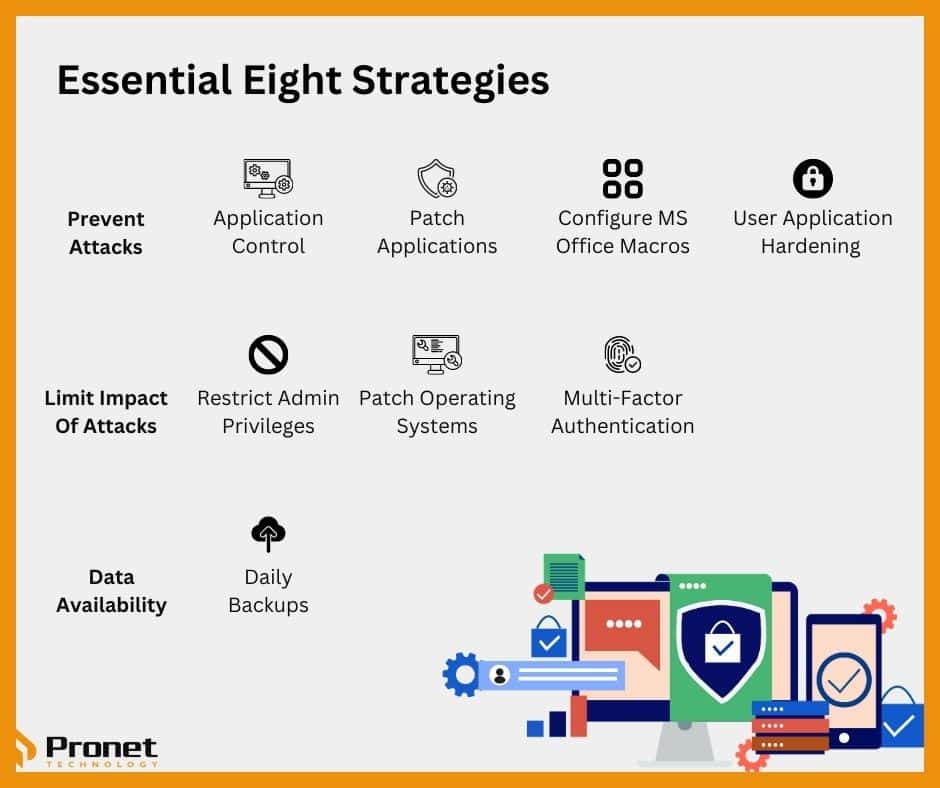
Essential Eight is a list of eight security strategies that ACSC believes will provide a strong foundation for Cyber Security. The strategies are based on ACSC’s experience and expertise in dealing with cyber threats and are designed to be effective against a range of cyberattacks, and they cover three key areas, prevention, limitation and recovery, and these are ranked by the business’ maturity level.
The strategies are not meant to be a one-size-fits-all solution, but rather a set of guidelines that businesses can use to tailor their security approach based on their specific needs and risk profile. By implementing Essential Eight, businesses can significantly reduce the risk of cyberattacks and protect their sensitive information and assets.
The Essential Eight strategies include:
- Application control: Allowing only approved applications to run on systems, preventing the execution of unauthorised software.
- Patching applications: Keeping all software up to date with the latest security patches to prevent exploitation of known vulnerabilities.
- Configuring Microsoft Office macro settings: Blocking macros from the internet and allowing only approved macros to run on specific systems.
- User application hardening: Configuring web browsers to block malicious content and implementing security features such as two-factor authentication.
- Restricting administrative privileges: Limiting the number of accounts with administrative privileges to minimise the risk of privilege misuse.
- Patching operating systems: Keeping operating systems up to date with the latest security patches to prevent exploitation of known vulnerabilities.
- Multi-factor authentication: Requiring additional forms of authentication, such as a security token or biometric authentication, to access sensitive information.
- Daily backups: Conducting daily backups of important data to ensure that in the event of a cyberattack, data can be restored to a previous state.
Implementing these strategies can seem daunting, but businesses need to protect themselves from cyber threats. Not only can a cyberattack cause significant financial damage, but it can also damage a business’s reputation and erode customer trust.
Do businesses need to report security breaches?
All Australian businesses with an annual revenue of $3 million are required to report data breaches both to impacted customers and to the Office of the Australian Information Commissioner (OAIC) within 72 hours. Since it’s difficult to gauge the impact of each breach, it’s best to report all breaches to be safe.
All health service providers, credit reporting bodies, credit providers that process credit eligibility information, Tax File Number recipients and all entities regulated under The Privacy Act 1988 must comply with this law, known as the Notifiable Data Breach Scheme (NDB).
This is required regardless of whether a business has implemented Essential Eight. The Essential Eight strategies simply provide a framework for businesses to prevent breaches and a way to protect themselves when one does occur.
Failure to report breaches The Privacy Act and can result in enforcement action. Businesses face a maximum fine of $1,800,000 for serious or repeated interference with an individual’s privacy.
Businesses need to ensure they have planned adequately for any potential data breaches, such as by reviewing their existing processes around data and Cyber Security and improving these by implementing Essential Eight. They also need to review their contracts with key suppliers to learn about how information is to be handled, as well as educate their staff on data breach laws and security practices, create data breach management strategies and consider Cyber Insurance to protect themselves against financial loss.
Essential Eight was created to provide a framework for businesses to protect themselves from cyber threats. By implementing these strategies, businesses can significantly reduce their risk of a successful cyberattack and safeguard their sensitive information and assets. Businesses need to understand the importance of Essential Eight and take steps to implement these strategies as part of their overall Cyber Security approach.



